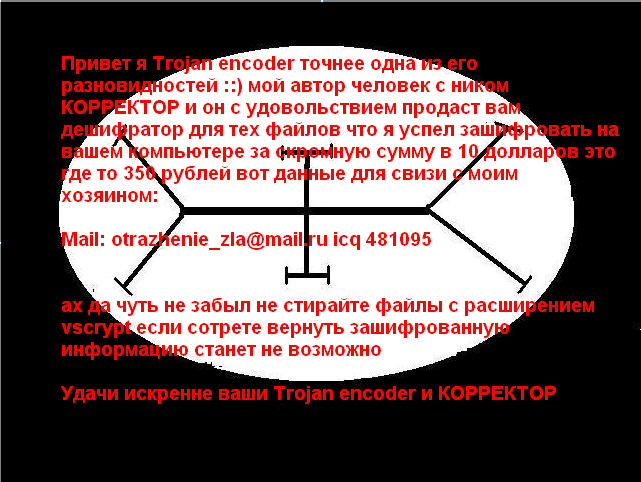
I recently got an important clue how the ransom exchange takes place between a victim and cyber criminals. One of readers who became a victim of this ransomware dropped an email to the author at the address otrazhenie_zla@mail.ru for his files to be recovered. This was the response by the author:
"Transfer into account pay pal 50 dollars here email pay pal otrazhenie_zla@mail.ru'
Interestingly, instead of asking him for the standard $10 ransom (as mentioned in his earlier message) he asked him for $50 - typical criminal mentality, isn't it? Unfortunately his greed doesn't end here. This malware instance came bundled in a fake 'SWF video codec' file. Upon execution, this setup file installs three different pieces of malware on the victim machine including this ransomware.