.., it's the size of the fight in the dog" that matters. Bredolab is not giving up. This morning, I found two more active CnC domains, not only alive but issuing new commands as well. These two domains are :
upload-good.net and lodfewpleaser.com
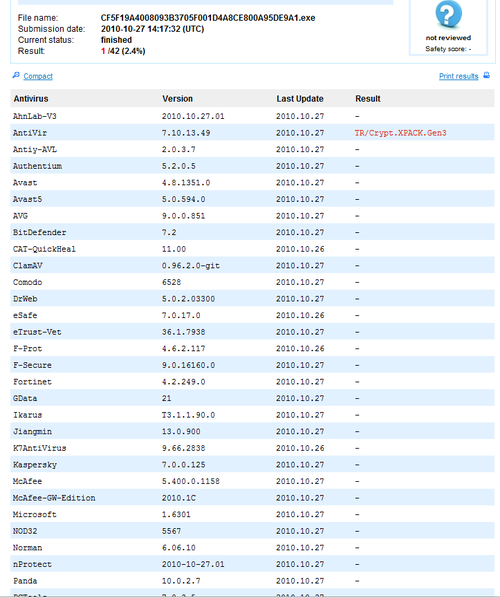
The Bredolab variant communicating to upload-good.net is especially important as almost all AVs are missing it at the moment. Only 1 AV out of total 42 AVs available on VirusTotal was able to detect it as malicious.
Here is the complete report 0ED70FA957EAD4D37A3851BF616E9832.
Let's put together all known facts and try to find out what's happening at the moment.
1. upload-good.net
This CnC is fully active and currently issuing new commands as normal. At the time of writing this article I can see that Bredolab is instructing it's zombies to download a Rogue Anti-Virus called 'Antivirusplus'. Currently this domain is resolving to 193.105.207.130. This IP belongs to a colo in Kazakhstan.
organisation: ORG-AL150-RIPE
org-name: Alfa-Host LLP.
person: Romanov Artem Alekseevich
phone: +75.332211183
address: Kazakhstan, Karagandinskaya obl, Karaganda, ul. Erubaeva 57, 14
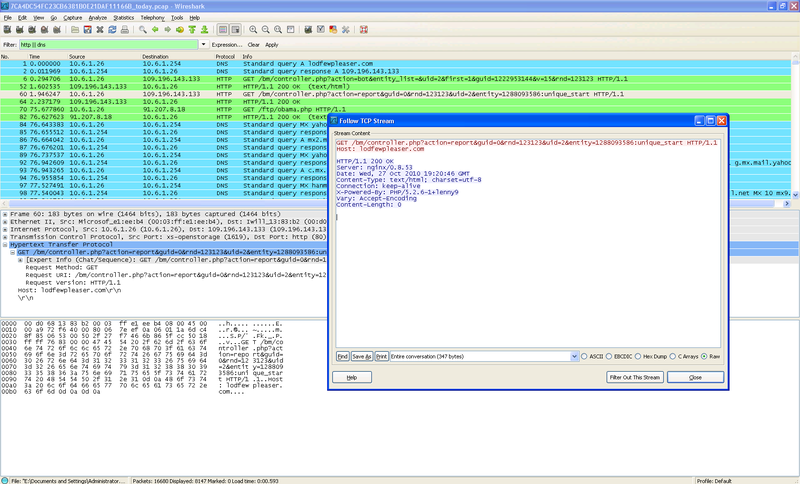
2. lodfewpleaser.com
This domain is fully active as well and currently instructing its zombies to send spam. This domain is currently pointing to 109.196.143.133 , and this IP belongs to the same colo in Russia that I mentioned in my last article.
nic-hdl: VN477-RIPE
mnt-by: VLINERU-MNT
source: RIPE # Filtered
person: Vyacheslav V Knowles
address: Russia, Moscow
address: Butlerova str, d.7
phone: +7 495 6642298
fax-no: +7 495 6642298 ext.5
3. proobizz.cc
This domain as mentioned in my last article is still alive. I am monitoring this domain very closely since yesterday. Around 6:40 AM PST today this CnC suddenly stopped issuing commands. Things changed around 1:30 PM PST today, when I started seeing the bot herders issuing new instructions. I am pretty sure that the bot herders behind this variant are fully active and probably not the guy arrested by the Dutch police yesterday. There can be two possible explanations for this:
1. The Bredolab code was leaked at some point and some other person started using it to build his own botnet. This is not so unusual. According to some confirmed sources, Cutwail (a famous spam botnet) code was leaked when one of the developer left the original bot herder's team and started building his own botnet. That's the main reason we see different variants of Cutwail in circulation.
2. At some point in time, a portion of Bredolab was leased out to some other gang.
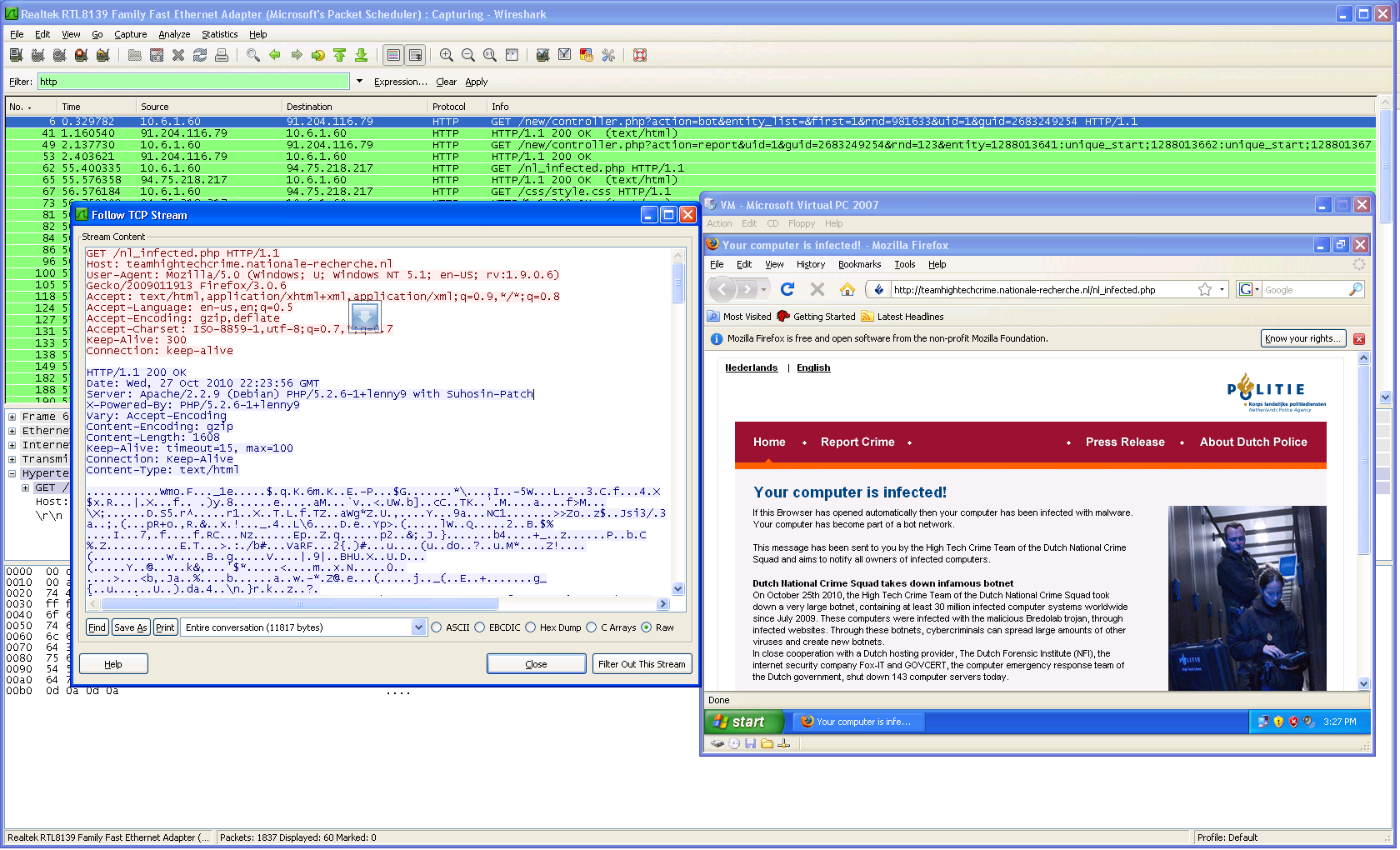
If you are wondering how it looks when the Dutch police's warning page automatically pops up onto the infected machine, here is a screen shot from a variant communicating to the CnC ds.meethomes.com (apparently under the control of Dutch Police).
No doubt some of the bot herders are still untouched and committed enough to continue their operations even under this extra scrutiny. This can also be confirmed from other sources:
1. News has just arrived that the Dutch police are hunting for more criminals behind Bredolab and that this crackdown operation is not over.
2. Symantec is also reporting that Bredolab is alive although the malware shown in their article is not the Bredolab we are talking about here, but Sasfis/Oficla (another powerful downloader). It's likely that Bredolab is sending spam to spread Sasfis. So at most there is a PPI or parent/child relationship. Rodel Mendrez from M86 Security had the same concern and also agrees that what is being shown in Symantec's article is Sasfis.
Regardless of this confusion it's sure that a small portion of Bredolab, even under so much stress, has been able to survive.
Atif Mushtaq @ FireEye Malware Intelligence Lab
Detailed Question/Comments : research SHIFT-2 fireeye DOT COM