
Ransomware Defense Assessment
Evaluate your ability to prevent, detect, contain, and remediate a ransomware attack
You do all you can to keep ransomware from getting into your environment, though you know that by large, compromises are still inevitable.
Mandiant’s Ransomware Defense Assessment evaluates your organization’s ability to detect, contain, and remediate ransomware within your environment—before it produces costly harm.
On Demand Webinar
Proactive Solutions to Stop Ransomware
Overview
The Ransomware Defense Assessment evaluates your environment for vulnerabilities exploited by modern, rapidly evolving ransomware attacks, as seen on the front lines of Mandiant’s incident response engagements. Our experts achieve this by assessing the impact a ransomware attack could have on your internal network, discover what data could be jeopardized or lost, and test the ability of your security controls to detect and respond to a ransomware attack.
This assessment will help you:
- Identify specific assets that ransomware can reach
- Realize security weaknesses that can be exploited by ransomware
- Minimize the impact of ransomware attacks
- Reduce your organization’s ransomware attack surface
- Recognize operational deficiencies in the management of ransomware-related risks
What you get
A detailed report including:
- Executive summary outlining key strengths and weaknesses of your security controls
- Technical details of testing performed
- Detailed findings, categorized by severity
- Executive briefing
Real attacks. Real learning. Real improvement.
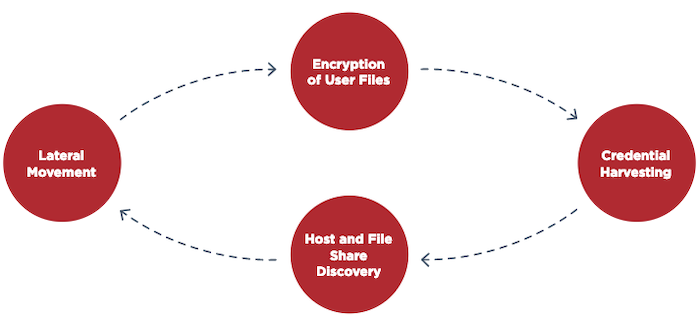
The Ransomware Defense Assessment simulates real-world ransomware by:
- Scanning for vulnerabilities exploited by ransomware
- Scanning for files accessible to ransomware
- Simulating lateral attack movement
- Simulating ransomware encryption
- Performing techniques used by threat actors to deploy ransomware
- Scanning for points in which
ransomware can spread across environments such as:
- Manufacturing and plant networks
- Backup infrastructure network
- Retail network
- Other secure networks
Related resources
Case Study
Ransomware and Incident Response Solutions
Tales from the Trenches
Ransomware Insured
Blog
Head Fake:
Tackling Disruptive Ransomware Attacks
Report
M-Trends 2020
Ready to get started?
Our security experts are
standing by to help you with an incident or answer questions about
our
consulting and managed detection and response services.
